Android DeviceManagement
Android device management refers to the process of managing, securing, and distributing devices running the Android operating system in a corporate setting. Some of the common tasks include, enrolling devices, enforcing security policies, installing apps, remotely wiping stolen or lost devices, and monitoring device usage and health. Android device management can be implemented using mobile device management (MDM) software or through the Android Enterprise platform, which provides a set of APIs and tools for managing Android devices in the enterprise. The main goal of Android device management is to keep devices secure and compliant with corporate policies, while also providing frontline workers, employees, and other users with the tools and resources they need to be productive.
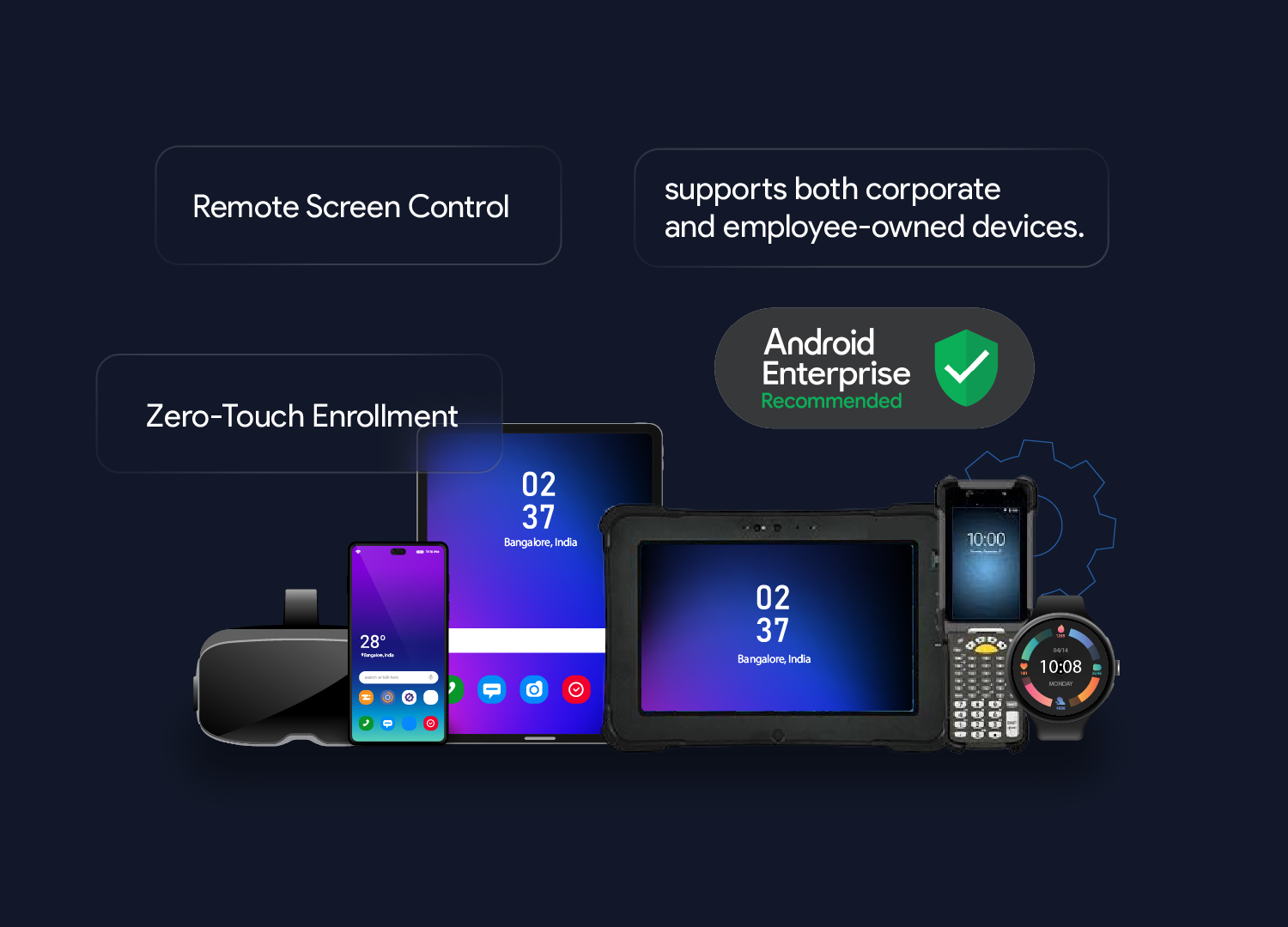
Android devices dominate the mobile device market. Businesses are using Android-based tablets, smartphones, rugged devices, smartwatches, and virtual reality devices for work purposes. Whether these devices are brought into the workplace by the employees (BYOD) or they are corporate-owned, there are many challenges in securing, monitoring, and managing these devices.
Android device management refers to the process of managing, securing, and distributing devices running the Android operating system in a corporate setting. Some of the common tasks include, enrolling devices, enforcing security policies, installing apps, remotely wiping stolen or lost devices, and monitoring device usage and health. Android device management can be implemented using mobile device management (MDM) software or through the Android Enterprise platform, which provides a set of APIs and tools for managing Android devices in the enterprise. The main goal of Android device management is to keep devices secure and compliant with corporate policies, while also providing frontline workers, employees, and other users with the tools and resources they need to be productive.
Android devices dominate the mobile device market. Businesses are using Android-based tablets, smartphones, rugged devices, smartwatches, and virtual reality devices for work purposes. Whether these devices are brought into the workplace by the employees (BYOD) or they are corporate-owned, there are many challenges in securing, monitoring, and managing these devices.
Capabilities of Android Mobile Device Management Software
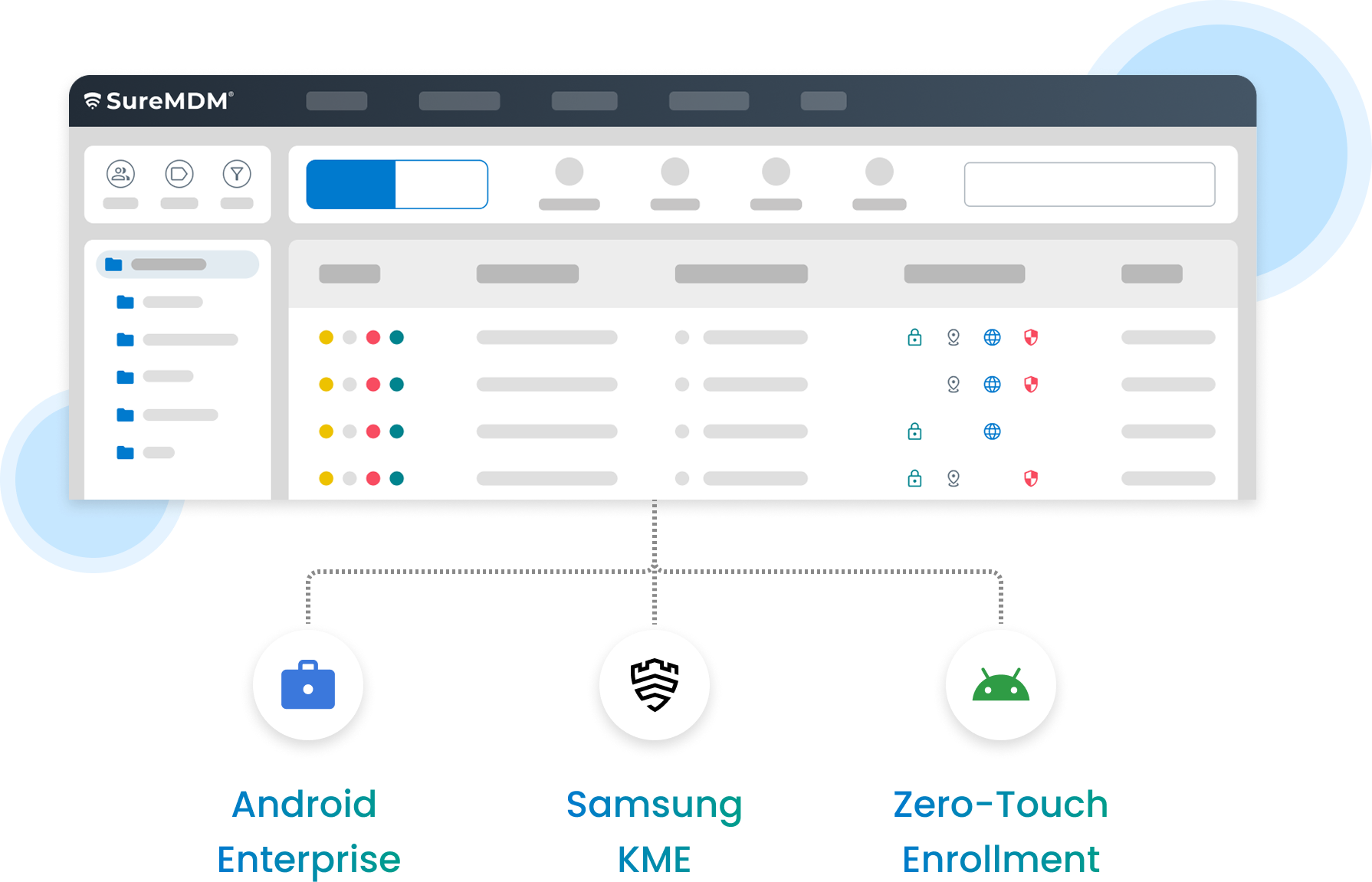
Android Device Enrollment
Installing Android Apps and Content
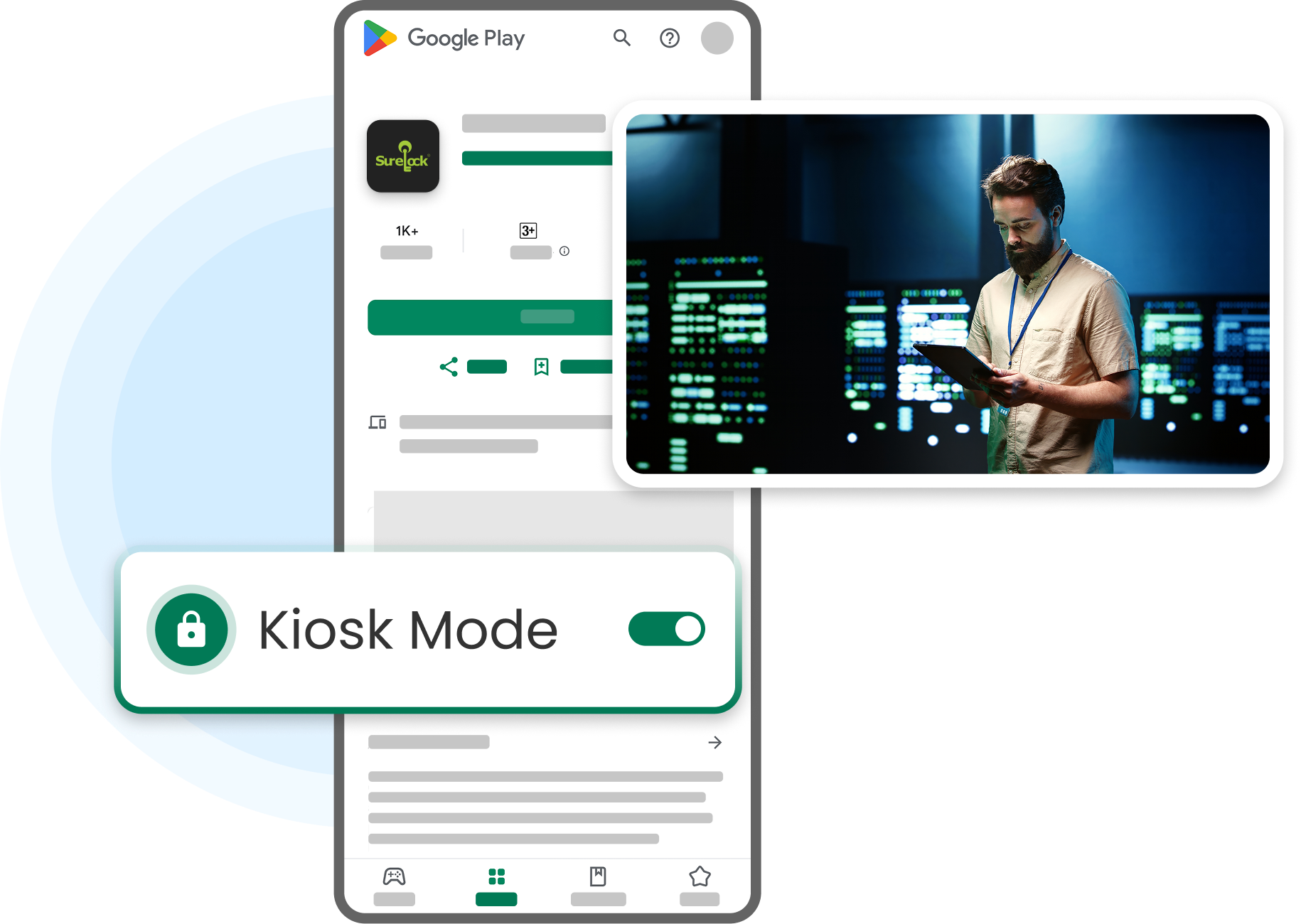
Secure Android Kiosk Mode
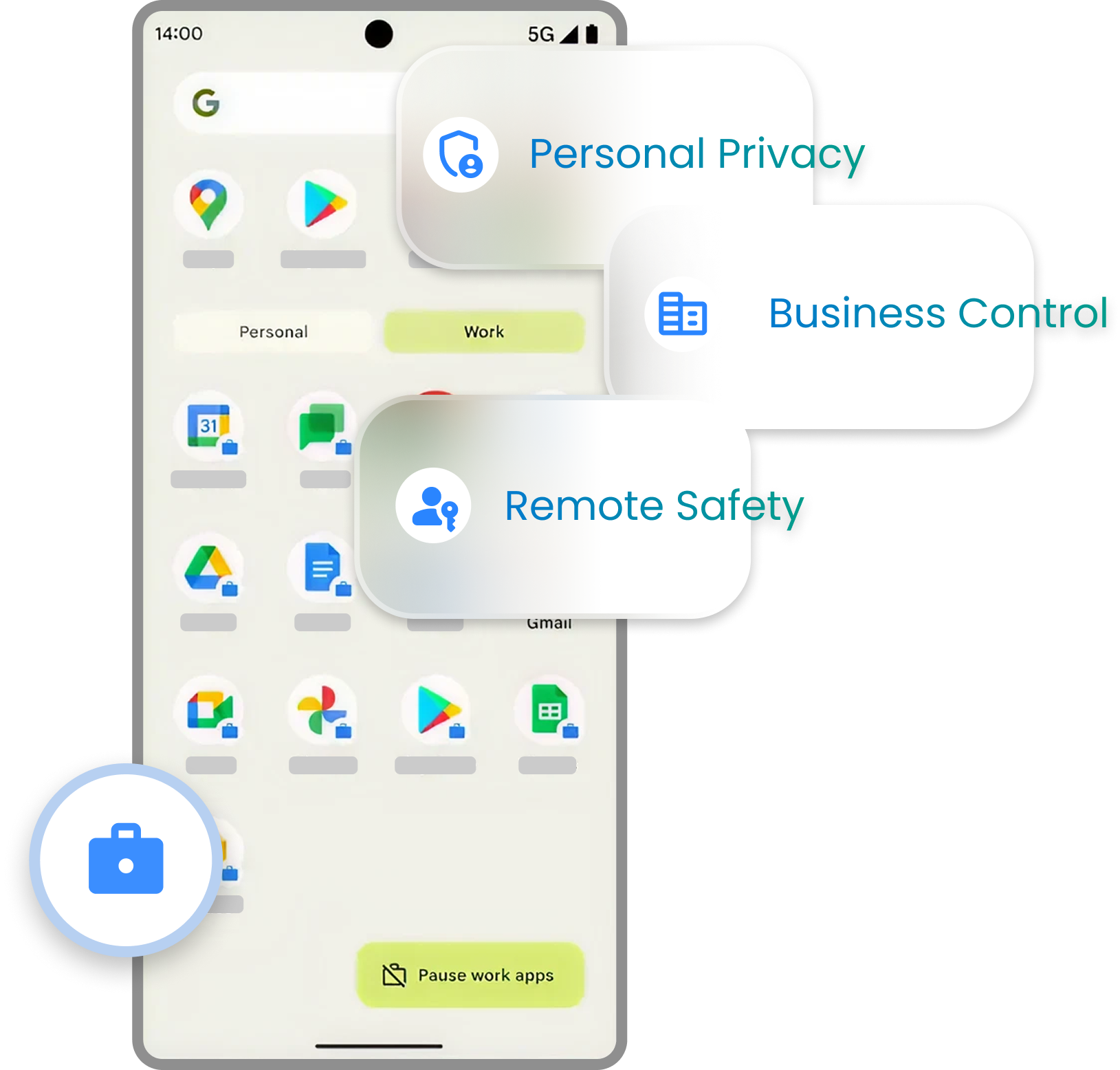
Profiles and Policies for Company-Owned and Employee-Owned Devices
Location Tracking
Troubleshooting Android Device Issues with Remote Control
Asset Tracking and Reporting
Android Device Management based on Device Ownership

Types of Devices Managed by Android MDM

Trusted Android MDM App Solution

What are the Features of Android MDM?
Manage Android Devices from a Central Console
Device Enrollment
Device Lockdown
Location Tracking
Remote Control
Messaging
Browser Lockdown
Asset Tracking
Device Maintenance Window
Mobile Application Management
Deploy, manage, and secure apps on devices
Enterprise App Store
Application Distribution
Mobile Content Management
Securely deliver data and keep it safe on devices



Android Enterprise
Remotely manage and secure your device fleet
Password Policy
Enterprise Email
Configure Applications
Enterprise Wipe
Enterprise Container
Container Encryption
Android App Restrictions
Bring Your Own Device (BYOD)
Bring Your Own Device (BYOD) is a corporate IT policy that allows employees to use their personal devices at the workplace. Employees can set up company email or access intranet websites on their personal phones or tablets. However, for IT, it is important to ensure that the data is safe and viewed only by employees. Various measures can be taken to achieve this goal.
Enforce Strict Password Policy
App Containerization
Enterprise Wipe
VPN Security
Wear OS Management
Remotely manage and secure smartwatches that run on Wear OS.


Android MDM FAQs
Here’s a list of common questions and answers related to Android mobile device management, which will help you understand what device management for Android is and how you can leverage it optimally.
Android MDM Trusted by IT Admins
Secure, Monitor, and Manage Your Android Device Fleet