42Gears WhitePapers
Your Roadmap to Digital Transformation
FIAM: Frontline Identity, Access, and Management
SureIdP: A Zero Trust Identity and Access Management Solution
Enhancing Logistics Efficiency and Security through Mobile Device Management with 42Gears
SureAccess: Next-Generation Zero Trust Network Access
25X your ROI with Mobile Device Management
App Wrapping vs. Platform Native Containerization: Which Mobile Application Management (MAM) strategy is better?
Controlling and Managing Privileged Access
According to Felix Gaehtgens, Research Director in Systems, Security, and Risk at Gartner,, "Privileged Access Management (PAM) is a crucial component of any security program because of the increasingly large scope of IT environments, privileged users, administrative tools, and Identity and Access Management (IAM) data such as passwords, encryption keys and certificates."
Retail in 2021: A New Variation on Retail 4.0
Before COVID-19, observers could trace a clear progression through Retail 1.0, 2.0, and so on, up to Retail 4.0.
However, consumer trends have changed so significantly as a result of COVID-19 that Retail 4.0 doesn't accurately describe the industry right now. Retailers now deal with unique circumstances exclusive to 2021.
In a time when in-person interactions are difficult, companies are in many ways less personal and more abstract than ever in the eyes of consumers.
Wi-Fi and Credit Card Data: A Risk You Can and Must Mitigate
One of the most vulnerable aspects of any organization is its Wi-Fi connection. Eavesdroppers want to intercept sensitive data as it travels from one endpoint to another. On a wired connection, this is difficult for an outsider to do. On a wireless network, it's much easier.
42Gears has extensive experience helping companies comply with PCI DSS standards. We've taken the time to summarize what we think is important, and what you can do to get started complying with PCI DSS standards.
Mitigating Android Security Vulnerabilities on Company-Owned Devices with 42Gears' UEM Solution
The Definitive Guide to Kiosk Management II
The Definitive Guide to Kiosk Management
Hardening Windows 10 Based Kiosks
Today, kiosks have become popular business tools for many reasons, including improved customer interactions, quicker service, reduced manpower requirements, reduced operational costs and many more. However, the increase in the number of cyberattacks in the recent past has made it clear that businesses not careful enough can fall prey to such incidents. Cybersecurity threats have become far too common and attackers often come up with newer ways to target different types of business endpoints, and interactive kiosks are no exception.
In order to complete transactions being carried out by customers, these kiosks gather personal and sensitive user information, which makes them attractive targets for hacking and ransomware attacks.
UEM Privacy and Data Protection Overview
Protecting Android Point-of-Sale (PoS) Devices with 42Gears UEM
The adoption of Android-based Point-of-Sale (PoS) devices across industries is on the rise due to the numerous advantages they have over manual or legacy systems, such as cost-effectiveness, easy software updates, better security, manageability, portability, better integration with third-party software and more. These PoS devices feed data to central systems, which in turn provide a good overview of the business and keep a record of the financial status, inventory, sales and automate multiple tasks, saving businesses a lot of time and effort, while reducing errors.
This paper explores the various PoS threats and security measures to safeguard PoS terminals and devices by offering application control and system hardening.
42Gears Mobile Application Management (MAM)
Today, mobile applications are a key component connecting employees to enterprise resources and ensuring team collaboration. These mobile apps not only help organizations increase productivity and efficiency, but also gain a competitive advantage by being agile. However, the sharp increase in the use of mobile devices and apps have posed quite a few challenges for IT pros. Since these apps provide easy access to corporate information on devices, they make corporate data vulnerable to threats. These vulnerabilities may be caused due to lack of encryption, data leakage during data synchronization, unauthorized access and/or poor data storage. To avoid such risks, businesses must ensure that these applications are secure and compliant with applicable policies.
This paper talks about how 42Gears offers a Mobile Application Management (MAM) solution to help enterprises distribute, deploy, manage, track and secure apps in a simplified way.
How Windows 10 will be a Game Changer for Enterprises
Microsoft Windows has evolved from a PC OS (Windows 3.1, Windows 95, 98) to a LAN/Network OS (Windows 3.11, Windows NT) and then to an enterprise-centric OS (Windows 10). Currently, Windows is the dominant operating system in enterprises across the world, with many organizations upgrading to Windows 10 for security and privacy reasons. Especially with support for Windows 7 ending in 2020, enterprises will have to make this shift immediately. However, more importantly, organizations must embrace Windows 10 to offer the modern workforce a smooth enterprise mobility experience.
This paper talks about how Windows 10 is paving the way for a new era of enterprise mobility.42Gears Mobile Email Management
Emails are an integral part of every business. Although other modes of communication, such as instant messaging, text messaging and social media, have emerged and are fast gaining popularity, emails continue to be the primary means of official communication. According to an Email Statistics Report 2017-2021 by Radicati Group, the number of email users worldwide will exceed 4.1 billion by the end of 2021. In 2017, the number of business and consumer emails sent and received per day was expected to reach 269 billion.
This paper talks about comprehensive features 42Gears Mobile Email Management (MEM) offers to safeguard corporate email infrastructures against threats.
42Gears Support for Office 365
Google and Microsoft have introduced cloud-based productivity tools (G-Suite and Office 365 respectively) to cope with problems related to on-premise setup. And an increasing number of organizations are migrating to cloud-based tools due to their cost-effectiveness and ease of management. Today, Microsoft's Office 365 is considered to be the most trusted cloud-based solution. With over 120 million business users, it has become the most adopted solution.
This paper talks about how Office 365 offers productivity tools to businesses to enable team collaboration, benefits and authentication methods for deployments.
Why integration of Mobile Threat Defense (MTD) solutions with EMM makes sense?
As businesses are adopting sophisticated mobile devices, operating systems, apps, and networks, they all are becoming vulnerable to different security threats such as malware, phishing, network attacks and man-in-the-middle attacks that are hard to detect and prevent.
This paper attempts to understand the security threats has increased exponentially that comes with rise in the adoption of sophisticated technology, enhanced work arenas and incorporation of new forms of endpoints such as IoT and Wearables.
Is your business ready for GDPR?
This paper attempts to help businesses understand how GDPR will work and making them aware of the harsh consequences of non compliance with the new law. It offers an analysis of how GDPR will bring consistency in business models and standardize the operations. It will also help individuals ascertain data privacy rules while embracing technological innovations.
Demystifying Mass Device Enrollment Programs
How is Enterprise Mobility Management (EMM) Impacting Banking, Financial Services and Insurance Companies?
Understanding Unified Endpoint Management
How Artificial Intelligence is Redefining Enterprise Mobility?
Drive Business Value from EMM Data using Mobile Analytics
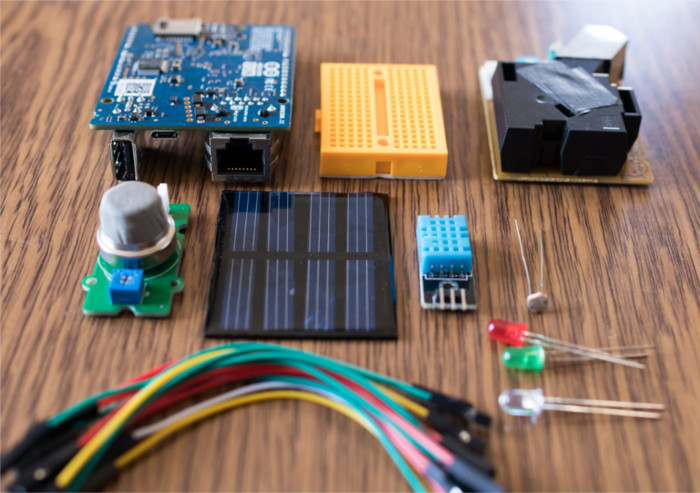
Building IoT Solutions with Managed Raspberry Pi
Internet of Things (IoT) is no longer experimental, it is a mainstream strategy. Raspberry Pi has emerged as a small budget-friendly computer that has laid the foundation for several IoT projects. Read this white paper to understand the benefits of IoT in business scenario, learn about IoT projects supported by Raspberry Pi and explore about possibilities on how an IoT ecosystems can be managed with an EMM solution.
Evolving Trends in Rugged Mobile Computing
Rugged Mobile Computing landscape is witnessing major changes due to the emergence of Android platform. This paper describes the pre-Android rugged handheld landscape, where Windows-based rugged devices were the market leaders. However, the uncertainty around support for Windows Mobile and CE is making feature-rich Android a preferred choice of building rugged handheld devices.
How Internet of Things (IoT ) is impacting Life Sciences and Healthcare Industry
EMM Shaping the endpoint security and management for Logistics and Transportation Industry
Now, growing complexities in logistics and transportation industry, as well as an increase in customer expectations, has created a need to adopt emerging technologies such as IoT (Internet of Things), cloud-based Transport Management System (TMS), unmanned aerial & ground vehicles, and wearables. These innovations might prove to be a boon to this Industry where time and efficiency define profit. Yet, implementing them into real practice need lots of improvement which is crucial for commercial adoption and their integration with EMM is also vital.