Enterprise Mobility Management | Mobile Application Management
Mobile Application Management
Distribute and control mobile applications on employee or company owned devices
With the increasing use of employee personal devices (BYOD) to access business data, mobile application management (MAM) policies offers enterprises with a secure and flexible approach to manage mobile apps and data while reassuring employees that their personal content will be protected and untouched.
42Gears offers Mobile Application Management (MAM) solution through its EMM suite. It enables management and distribution of mobile applications through Enterprise App Store functionality.
With 42Gears MAM, enterprises can remotely distribute and control mobile apps through a web-based console. MAM functionalities facilitate a variety of tasks such as administrative push, updating custom and public (app store) apps, and management of associated app licenses. IT admins can remotely apply management and security policies such as data encryption and data storage of apps. 42Gears MAM also allows to selectively wipe apps and any associated data from the device as per requirement.
MAM Features
Application Distribution

Remotely push apps and updates from the MDM dashboard to enrolled mobile devices.
Distribute applications based on all or a set of users.
VPP (Volume Purchase Program) support on iOS.
Enterprise App Store

Deploy in-house-developed and commercially sourced applications.
Manage Google Play
Private App Store.
Provide full app-lifecycle support powered by cloud-based platform.
App Management
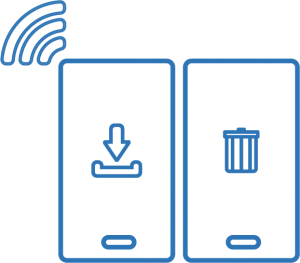
Remotely install or uninstall any apps.
Push notifications and updates to your apps.
Restrict app access based on user role.
Get detailed report on
deployed apps.
Remove or Uninstall corporate applications selectively when an employee leaves the organization or loses a device.
MAM Benefits

Protect corporate data, irrespective of device ownership
- Enhance authority and limit access as per hierarchy structure.
- In BYOD, containerization policies keep employee data and personal data separate.

Improves Operational efficiencies
- Data gathered on user behavior from endpoints can help decision makers take informed decisions.

Reduces IT support required for the Applications Update
- Application upgrade prompts are sent to users and maintenance is scheduled automatically.
- Automated processes can help IT staff focus on other initiatives to drive value for the organization.
