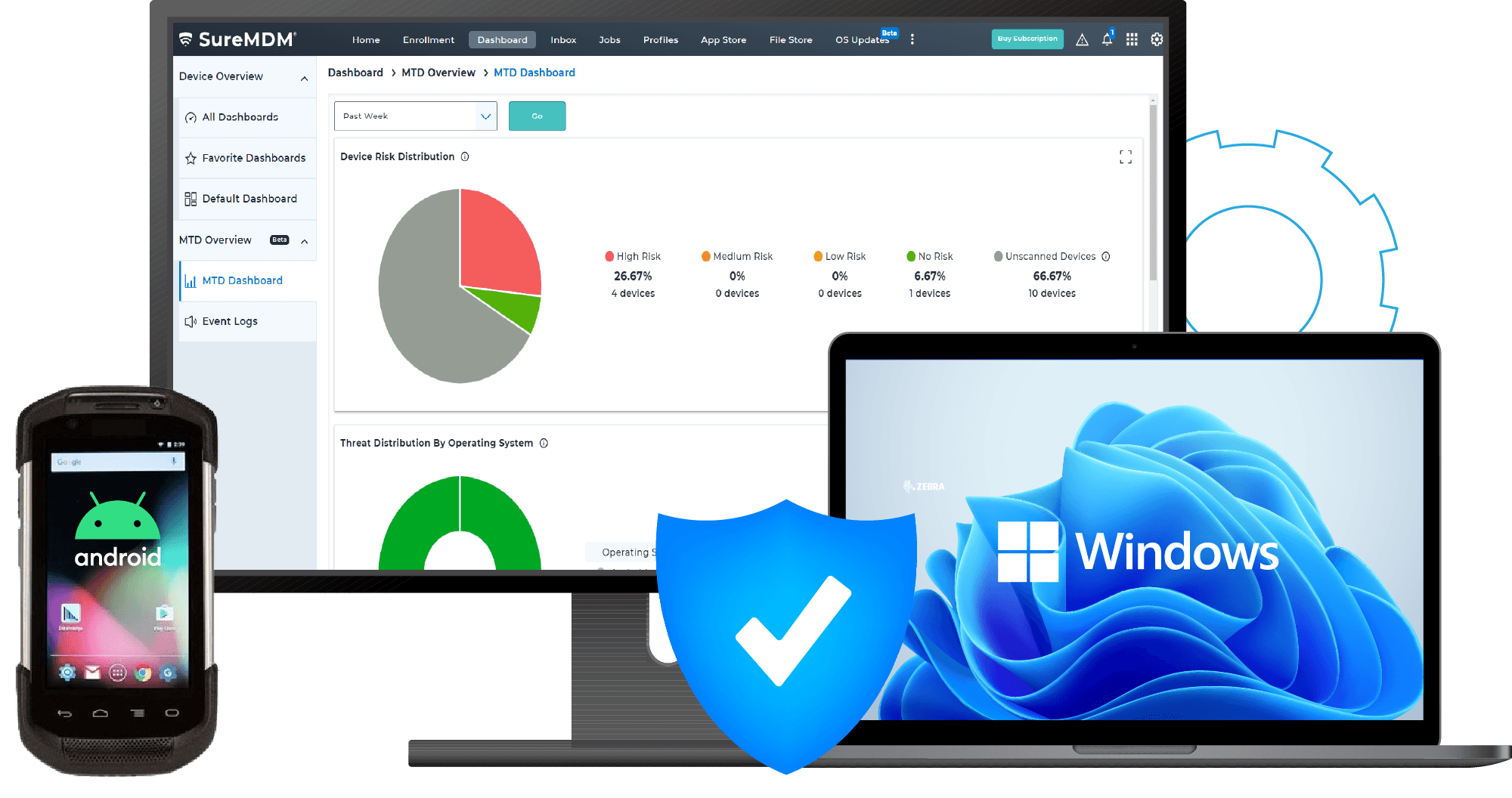
MTD - MobileThreat Defense Solution
Identify and eliminate security vulnerabilities
Overview
64% of mobile threats come from your apps, and that's not all- leakware is present in 35% of all installed applications. If you are looking to proactively safeguard your endpoints and business data from cyber threats, deploying an MTD (Mobile Threat Defense) solution can help!
MTD solutions strengthen mobile security by preventing, detecting, and remediating sophisticated cyberattacks using advanced techniques. When integrated with a UEM platform, this powerful combination ensures comprehensive security management and robust policy enforcement.
FAQs
Find answers to common questions about our service.