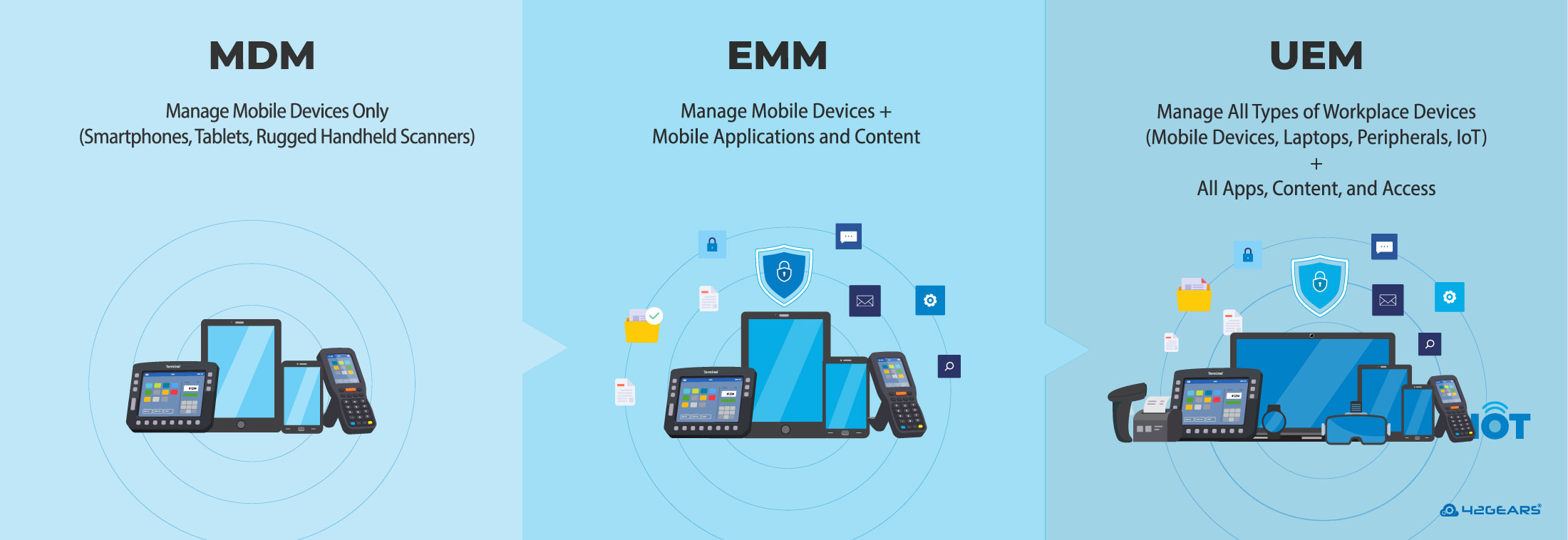
Managing mobile devices across business operations is more critical to enterprise success than ever before. Several categories of mobile security products like MDM (Mobile Device Management) and EMM (Enterprise Mobility Management) have emerged to address the problems related to data security and privacy. Here are few pointers which will explain the basic difference between these products:
MDM (Mobile Device Management)
It is all about remotely managing devices, allowing users to perform certain prescribed tasks on their phones and tablets. MDM includes features like device provisioning, enrollment, device security and location tracking. It also helps in wiping the data in case the device is stolen or lost. A basic MDM tool has the ability to enforce security policies, track inventory and perform real-time monitoring and reporting.
The Rise of BYOD
From a security standpoint, this was a perfectly reasonable way to manage a company-owned device. But some employees were not very comfortable carrying two separate devices for business and personal use. So it was in the interest of businesses to consider employees’ demand for BYOD (Bring Your Own Device). A single device that gave employees the flexibility and ease to shift from personal to work use, anywhere, and anytime.
Emergence of Mobile Application Management (MAM)
The rapid growth of the smartphones, mobile applications market, and the need for data security led to the creation of Mobile Application Management (MAM) solution that limited the management and control of specific business applications. Mobile Application Management is like MDM, except that it’s only applied to specific applications on a device instead of the entire device. MAM helps in creating an enterprise app store and pushing or updating necessary apps on business devices remotely. But sometimes MAM has its own set of challenges as well. Since every business app requires unique coding to work with each individual MAM product, the availability of apps for a specific standalone platform can be limited.
Beyond MAM: MIM and MCM Evolution
Nonetheless, MAM was a perfect settlement between employees and employers without compromising data security and interfering in employee privacy. But in practice, the experience was not so great as it cannot be easily extended to support the majority of native app-store applications. After that, there were several small development stages where the experience got redefined with the evolution of applications such as MIM (Mobile Information Management) and MCM (Mobile Content Management). They are focused on the security of a particular document repository where employees and employers access and share documents or files without affecting the entire device or other applications.
EMM (Enterprise Mobility Management)
And finally, it reached the stage of EMM. EMM is nothing more than the combination of an MDM and a MAM solution equipped with a secure container that keeps business data secure. An EMM solution in addition to MDM offers Mobile App Management, Mobile Content Management, App Wrapping, and Containerization. EMM is a complete package of services which offers complete data security on BYOD and Dedicated Devices (formerly called COSU or Corporate-Owned Single-Use) for enterprises.
BYOD and the Role of Containerization
While MAM and MDM solutions were going through continuous upgrades to match the growing needs of data security in enterprises, BYOD as a concept came into picture which allowed the end users to bring in their own mobile devices and get them enrolled into IT’s corporate resources. BYOD is enabled through the concept of containerization, letting the IT Admin segregate company and personal data on the same handheld. It helps the IT Admin create encrypted, policy-enabled and distinct containers in employees personal devices to use browser apps and deliver specific email and data.
Simply put, the main difference between MDM and EMM is that MDM manages all the features of the device while EMM manages the entire device. EMM provides policy compliance, app customization, data and document security, and incorporates into the network directory services.
UEM (Unified Endpoint Management)
As more enterprises become aware of the need to safeguard their networks and ensure data compliance, they are quickly switching from MDM to EMM solutions. As new progressive technologies make their way into the global market, the world is moving towards advanced mobility management solutions such as Unified Endpoint Management (UEM). UEM enables businesses to manage all endpoints such as laptops, mobile phones, tablets, PCs, printers, and wearables using a single comprehensive EMM solution.
MDM vs. EMM vs. UEM: Table Comparison
| Feature | MDM | EMM | UEM |
| Focus | Manages mobile devices | Manages devices plus apps and content | Manages all endpoints from one place |
| Device Support | Phones and tablets | Phones, tablets, and some laptops | Phones, tablets, laptops, desktops, IoT |
| Key Features | Remote lock/wipe, basic config. | Secure apps, email, docs | Full device control, Third-party integrations |
| Security Coverage | Device-level controls only | App-level security and data protection | End-to-end security across all devices |
| Automation | Limited automation | Some task automation | High automation with self-healing workflows |
| IT Efforts | Manual setup and updates | Moderate admin work | Low admin effort due to unified console |
| Integration with IT Systems | Minimal system integrations | Connects with common business tools | Works with most IT and security platforms |
MDM vs EMM vs UEM: Choosing the Right Mobility Solution
- MDM – Great for basic mobile security, ideal for smaller teams with less number of corporate-owned devices
- EMM – Suited for companies with BYOD policies and more app/data management needs
- UEM – Best for enterprises with a large fleet of devices
🌐 Real-World Use Cases
1. MDM for Field Services
Companies (Logistics and Last-mile delivery) with ruggedized, company-issued devices use MDM for tracking, remote wiping, and provisioning.
2. EMM for BYOD-Enabled Organizations
A marketing firm or educational institution enables staff to access emails and corporate apps on personal devices securely using EMM with app wrapping and containerization.
3. UEM in Healthcare
A healthcare enterprise manages laptops, iPads, workstations, and even smart medical equipment from a unified console using UEM—ensuring HIPAA compliance across devices.
📈 Why Businesses Are Moving to UEM
- Digital Transformation & Hybrid Work: UEM supports cloud-first strategies and remote workforces.
- Zero Trust Security Models: UEM enables context-aware access, identity-based controls, and device posture assessment.
- Device Diversity: From Android and iOS to Windows 11, macOS, Linux and even IoT endpoints—UEM covers it all.
- AI & Automation Integration: Modern UEM platforms now include AI-driven analytics, automated compliance enforcement, and self-healing capabilities.
FAQs
1. What is the main difference between MDM, EMM, and UEM?
- MDM (Mobile Device Management) focuses on managing and securing entire mobile devices.
- EMM (Enterprise Mobility Management) extends MDM by also managing apps, content, and data, supporting BYOD through containerization.
- UEM (Unified Endpoint Management) goes beyond mobile to manage all types of endpoints—laptops, desktops, wearables, and more—from a single platform.
2. Can small businesses benefit from UEM, or is it only for enterprises?
Yes, small businesses can absolutely benefit from UEM. While originally designed for large enterprises, modern UEM solutions are now more scalable, affordable, and user-friendly, making them ideal for small teams needing to manage multiple devices securely. It helps streamline IT tasks, reduce manual work, and enhance data protection—even with limited IT resources.
3. Are MDM, EMM, and UEM secure for remote work?
Yes, MDM, EMM, and UEM are all secure for remote work, but their level of protection and flexibility varies:
✅ MDM secures the entire device, making it suitable for company-owned phones and tablets in remote setups.
✅ EMM adds app and data-level security, ideal for BYOD scenarios where personal and work data need separation.
✅ UEM offers the most comprehensive security, managing all endpoints (including laptops and desktops), enforcing policies, and supporting Zero Trust models—perfect for hybrid and fully remote workforces.
Each solution enhances remote work security, but UEM provides the broadest protection and control across all devices.
4. Which solution is the best for BYOD (Bring Your Own Device) environments?
EMM and UEM are better suited for BYOD. They offer app-level controls and containerization to separate personal and work data.
5. How do MDM, EMM, and UEM help with compliance requirements?
MDM, EMM, and UEM solutions help businesses meet various compliance standards (e.g., GDPR, HIPAA) by ensuring devices and data are properly secured, controlled, and monitored. UEM, especially, simplifies compliance across diverse endpoints.