🚧 Page Under Maintenance
Some sections are currently being updated. Content mapping is in progress and will be available soon.
Cisco
Combining Mobile Device And Network Management To Restrict Unsecured Mobile Devices
Know More Try SureMDM for FreeOverview
As mobility technologies mature, cybersecurity risks also become more complex. Threat vectors mostly target devices and networks. Thus, businesses need to take appropriate measures to avert threats to both comprehensive Mobile Device Management and Network Management.
Cisco & 42Gears’ Partnership
42Gears, a leading unified endpoint management solution (UEM) provider has now become a Cisco® Solution Partner by integrating its flagship solution SureMDM with Cisco Identity Services Engine (ISE).
42Gears and Cisco have come together to address the challenges such as
- Threats due to weak mobile device management and network compliance.
- Manual process for device and network compliance which results in non-optimization of resources.
- Manage a mix of employed owned (BYOD) and company-owned mobile devices
42Gears is now a part of Cisco’s Solution Partner Program. SureMDM enables Cisco ISE to make intelligent network admission decisions by providing information about the configuration and security state of mobile devices. Cisco ISE assigns network access privileges based on user credentials, attributes, and device security information.
The Integration
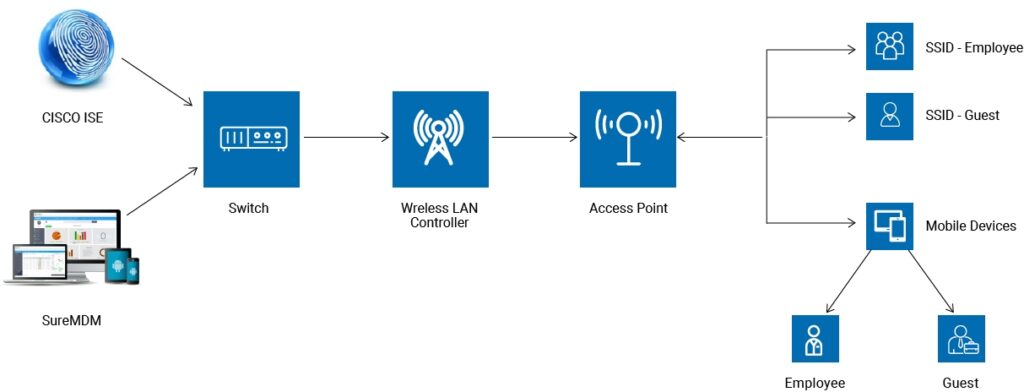
Network Architecture of SureMDM & Cisco ISE Integration
SureMDM and Cisco will make the synchronization process fast, efficient, and secure.
Below are the 3 steps for integration:
![]()
Device makes connection request to Cisco ISE
![]()
Device enrollment and compliance check is done by SureMDM.
![]()
SureMDM conveys to Cisco ISE that the device is safe and secure.
Integration Features
![]()
Registration
Non-registered devices trying to access the network will be redirected to the registration page for registration based on user role, device type, etc.
![]()
Restriction
Non-compliant devices will get restricted access based on the state of compliance
![]()
Compliance Check
Perform periodical compliance checks with SureMDM
![]()
Remote Management
Cisco ISE admins can perform remote actions using SureMDM (such as wiping a device if it is lost or stolen)
Benefits to Everyone
![]()
For Cisco
Restricting non-compliant devices from getting connected the network and threats posed by such devices

For 42Gears
Enhance the compliance and management of devices.
![]()
For IT Admin
- Get to know the device’s security and compliance state
- Enforce and manage network policies for specific or group of devices
- Control guest and device access
- Easily detect new devices and automate security policies
![]()
For End-Users
Freedom to choose the device i.e. company- or own and quickly gain network connection.
The integration helps enterprises in having enhanced network security, network and device policy compliance and grant privileges to mobile devices. Due to the integration, device security and network security are addressed adequately.