Why Integration of Mobile Threat Defense (MTD) Solutions with EMM Makes Sense
Author: 42Gears Team
As businesses adopt sophisticated mobile devices, operating systems, apps, and networks, they increasingly expose themselves to complex security vulnerabilities. Threats like malware, phishing, network sniffing, and man-in-the-middle attacks have become difficult to isolate using traditional corporate network defenses.
With the rapid integration of enterprise IoT, wearables, and field-ready tablets, this security perimeter continues to fragment. Hundreds of thousands of new mobile malware variants are discovered regularly, converting unpatched devices into active corporate data leaks.
Gartner Insight: Mobile malware and targeted platform exploits represent an ever-growing share of standard digital testing indices. Organizations must proactively move beyond basic device provisioning toward unified threat response frameworks.
This evolving landscape requires the inclusion of Mobile Threat Defense (MTD) platforms directly into digital business ecosystems. To manage risk effectively, companies are blending traditional configurations with continuous threat visibility, creating an integrated defensive standard.
Modern attackers target mobile operating systems directly because these devices bypass perimeter firewalls. Key threat categories include:
Advanced Target Spyware (e.g., Pegasus Class)
Highly sophisticated, enterprise-grade spyware targets mobile operating systems to silently extract data from voice communications, encrypted messaging apps, email archives, location logs, and onboard cameras without user interaction.
Mobile Botnets & Root-Level Malware
Malware campaigns can convert thousands of corporate smartphones into distributed botnets. Compromised systems route malicious traffic through proxy IPs or perform background click fraud, draining battery cycles and exposing local corporate networks.
SMS Phishing & Fraudulent Adware
Attackers leverage social engineering or SMS phishing to trick users into downloading sideloaded or credential-harvesting tools. Once inside the system, these malicious packages can intercept single sign-on (SSO) tokens.
Abandoned or "Dead" Applications
When apps are removed from public stores like Google Play or Apple App Store due to security non-compliance or lack of updates, any surviving installations on employee devices remain unpatched, offering a backdoor for network threat actors.
MTD tools actively defend enterprise-connected endpoints across three core vectors:
| Vector | Core Defense Mechanism |
|---|---|
| Device Level | Tracks low-level system parameters, firmware integrity, boot states, and configuration baselines to instantly flag privilege escalations or missing security patches. |
| Network Level | Monitors cellular and wireless traffic to block untrusted gateways, detect man-in-the-middle (MitM) attacks, flag spoofed certificates, and prevent SSL stripping. |
| Application Level | Utilizes reputation scanning, reverse engineering, static/dynamic code analysis, and behavioral simulation to catch leaky apps and zero-day mobile payloads. |
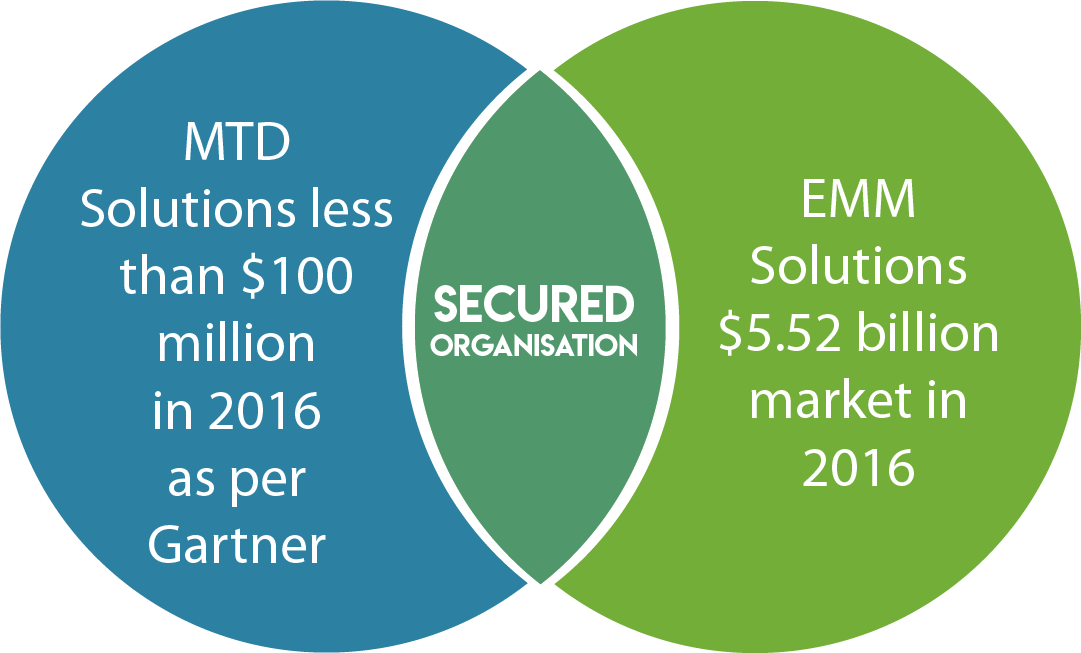
Traditional Enterprise Mobility Management (EMM) or Unified Endpoint Management (UEM) solutions focus heavily on identity provisioning, enforcement of device encryption, profile distribution, and data separation. However, EMM solutions are generally not designed to analyze live network anomalies or execute runtime code heuristics.
Integrating MTD with EMM bridges this gap. While EMM governs compliance policies, MTD provides behavioral threat data. Together, they enable automated, real-time remediation loops.
 EMM & MTD Collaborative Architecture
EMM & MTD Collaborative Architecture
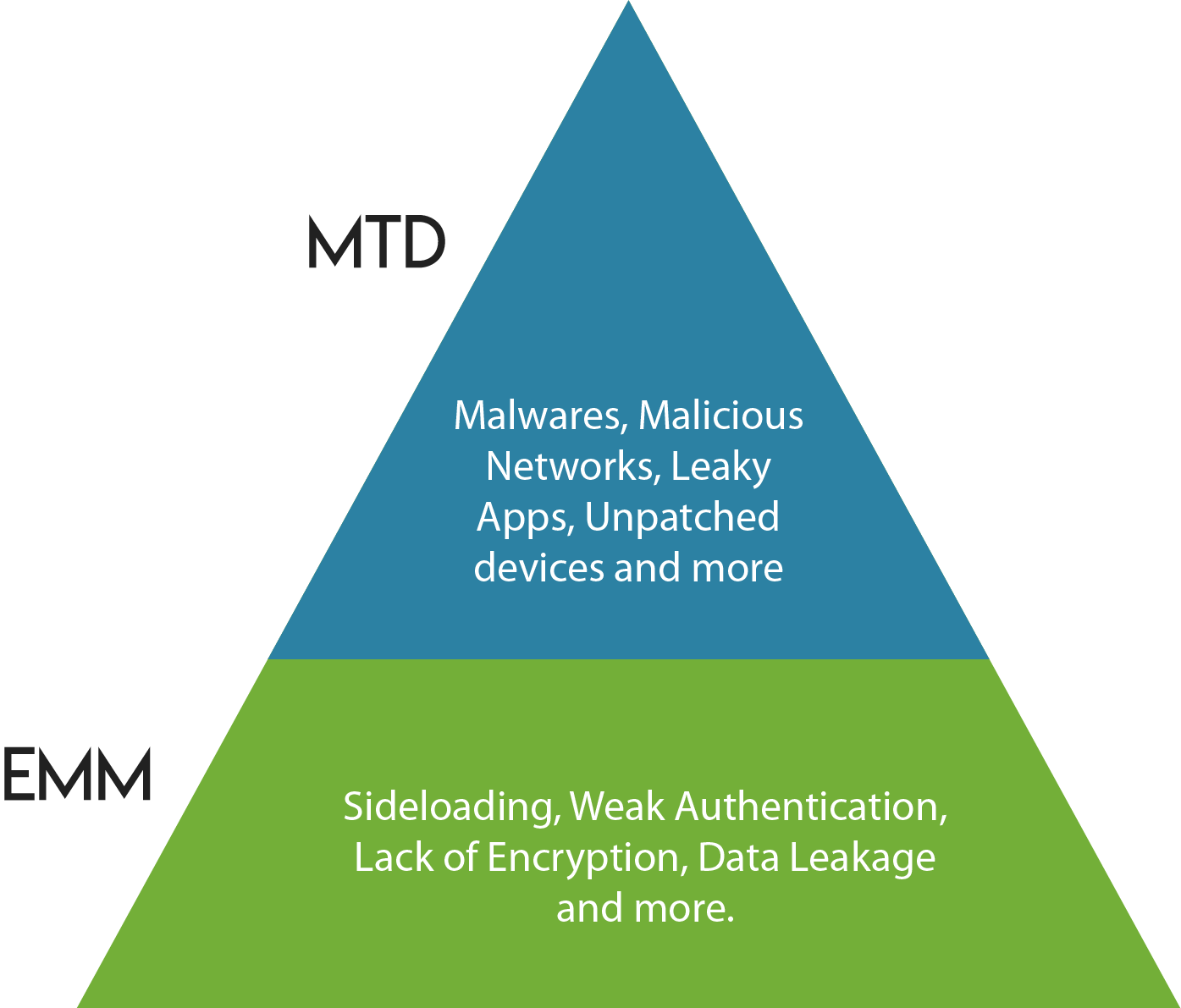 Functional Spectrum: UEM vs. Mobile Threat Defense
Functional Spectrum: UEM vs. Mobile Threat Defense
The integrated workflow functions as an automated loop that minimizes human intervention:
- The EMM platform deploys, configures, and secures the native MTD application across target endpoints using managed app configurations.
- The local MTD application constantly monitors the network layer, system binaries, and installed application behaviors.
- If a threat is detected, the MTD application alerts its central management server, which immediately signals the EMM server.
- The EMM server flags the device as non-compliant and instantly revokes access to managed profiles, enterprise email, internal apps, and corporate VPN gateways until the threat is removed.
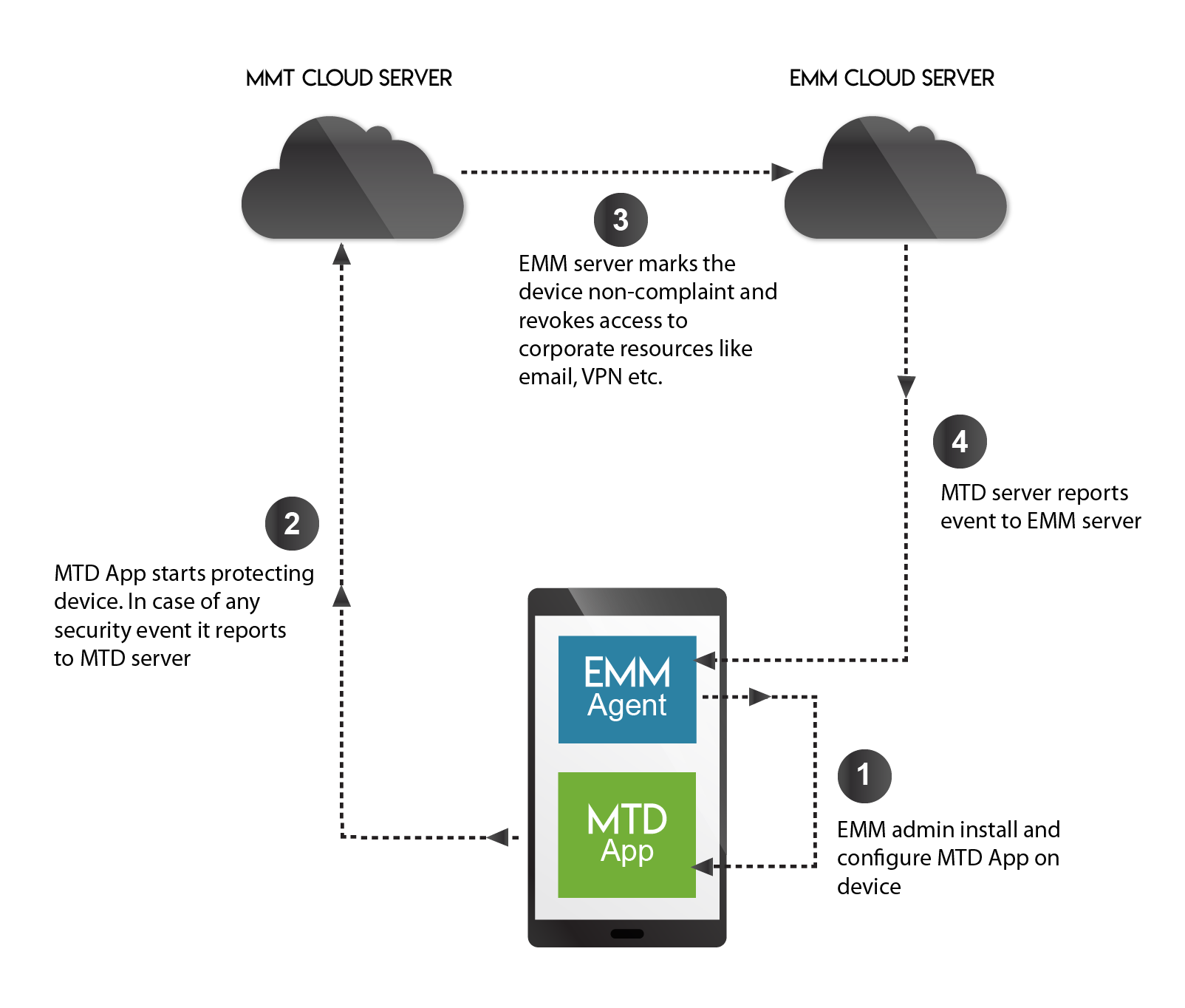 Live Threat Communication Loop between Cloud Environments
Live Threat Communication Loop between Cloud Environments
Organizations must evaluate several operational parameters when selecting an MTD partner:
- Specific industry compliance mandates (e.g., HIPAA, PCI-DSS).
- The distribution of mobile platforms (Android vs. iOS vs. Windows).
- Deployment strategies (BYOD vs. COPE vs. COBO).
- The programmatic capabilities and open API structures of the existing EMM platform.
| Vendor | OS Support | OS Level Attacks | Leaky Apps | Network Attacks | URL Filtering | EMM Sync | Deployment |
|---|---|---|---|---|---|---|---|
| Check Point | iOS, Android | Yes | Yes | Yes | No | Yes | App, SDK |
| Lookout | iOS, Android | Yes | Yes | No | Yes | Yes | App, SDK |
| Pradeo | iOS, Android, Win10 M | No | Yes | No | Yes | Yes | App, SDK |
| Symantec | iOS, Android | Yes | Yes | No | Yes | Yes | App, SDK |
| Wandera | iOS, Android, Win10 M | Yes | Yes | No | Yes | Yes | App, Proxy |
| Zimperium | iOS, Android, Win10 M | Yes | Yes | No | No | Yes | App, SDK |
Mobile fleet management and endpoint security are fundamentally linked. Integrating MTD with an EMM engine creates an adaptive defense system capable of stopping live exploits. This capability is critical for organizations operating in highly regulated fields like banking, insurance, and healthcare, as well as those managing extensive Android deployments.
42Gears integrates seamlessly with top MTD vendors, combining comprehensive UEM configurations with advanced threat intelligence to ensure your entire mobile endpoint workforce remains resilient and compliant against zero-day threats.
References & Industry Sources:
1, 3. Gartner Research: Market Guide for Mobile Threat Defense Solutions Framework.
2. CSO Security Analysis: Mapping Structural Realities of Distributed Endpoint Botnets.
Gartner Disclaimer: Gartner does not endorse any specific vendor, product, or service depicted in its research publications. Research represents internal analytical evaluations and should not be treated as absolute statements of fact.