What Is the 4 Eyes Principle and Why Your IT Team Needs It
Mar 17, 2026 | Nareddy Saivikas Reddy
Imagine this: An IT admin intends to perform a critical operation like wipe/delete on a single device. Due to a small selection mistake, the action request is accidentally sent to an entire device group instead of just one device. Within seconds, multiple company devices could be wiped, resulting in data loss, operational disruption, and potential compliance issues.
After the action is executed, there is often no easy way to reverse the impact. What began as a simple administrative task can quickly escalate into a large-scale operational issue affecting employees, business continuity, and data integrity.
Scenarios like this highlight the need for stronger admin access control and an additional verification layer before executing sensitive operations. To address this risk, 42Gears’ SureMDM has implemented the Four-Eyes Principle.
But what is the four eyes principle, and why is it becoming essential for organizations managing critical administrator access?
What is the Four-Eyes Principle?
The Four Eyes Principle (also known as the 4 Eyes Principle) is a control mechanism that requires two authorized individuals to complete critical actions. One person initiates the action (the Initiator), and another reviews and approves it (the Approver).
The core idea is simple:
No critical action should be executed without review and authorization from a second responsible party.
This approach significantly strengthens admin access control and reduces the risk of:
- Unauthorized changes
- Accidental execution of sensitive actions
- Insider threats
- Compliance violations
Why the Four Eyes Principle Is Important
As part of their day-to-day responsibilities, IT administrators perform a wide range of operations, including sensitive and high-risk actions such as device wipes, data deletion, and configuration changes. These actions can have irreversible consequences if executed incorrectly.
Without proper checks:
- A simple mistake can impact thousands of devices.
- A compromised account can cause severe damage.
- Compliance requirements may be violated.
The 4 Eyes Principle introduces accountability, transparency, and traceability, ensuring that every critical action is reviewed before execution.
How the Four Eyes Principle Works with SureMDM
The 4 Eyes Principle operates through structured role separation and an approval workflow.
When a user initiates a designated critical action:
- The action is not executed immediately.
- A request is generated.
- The request must be reviewed and approved by an authorized administrator.
- Only after approval is the action executed.
This ensures enhanced security and prevents unintended operations.
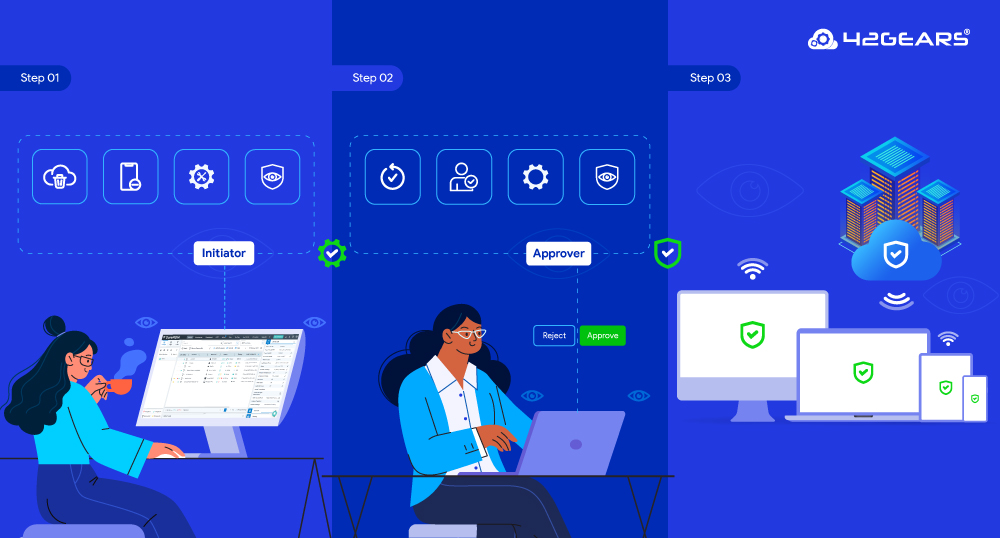
The Approval Workflow: Step-by-Step
Step 1: Initiator Initiates Action
- The Initiator initiates a critical operation, like remote wipe or device deletion from SureMDM
- A confirmation message indicates approval is required, and a request is created.
- A unique Request ID is generated.
- The assigned Approver receives a notification.
Step 2: Approver Reviews the Request
The Approver:
- Reviews the request details.
- Verifies the target device and intended action.
- Approves or rejects the request.
- Adds optional comments.
Step 3: System Updates Status
- Approved → Action is executed, status updated.
- Rejected → Action is cancelled, status updated.
- Notifications are sent to both Initiator and Approver.
All actions are recorded for audit and compliance tracking.
Best Practices for Implementing the Four Eyes Principle
- Limit Approver roles to trusted administrators.
- Regularly review approval logs.
- Avoid excessive self-approval configurations.
- Ensure timely review of pending requests to prevent workflow delays.
Final Thoughts
The Four Eyes Principle is more than just an approval workflow—it is an enterprise security governance model designed to protect organizations from operational, security, and compliance risks.
By separating action initiation from authorization, it ensures that every critical operation is reviewed, validated, and properly documented.
In an era where administrative actions can have massive consequences, the Four Eyes Principle stands as a simple yet powerful safeguard—because sometimes, two pairs of eyes are better than one.
Ensure every sensitive action
is verified before execution.
Subscribe for our free newsletter